Why is Autoblogging.ai the Best AI Writing Tool?
Looking to streamline your content production process without sacrificing quality? Look no further than Autoblogging.ai. This cutting-edge AI writing tool harnesses the power of artificial intelligence to produce well-crafted, SEO-friendly articles with astonishing speed and precision. Whether you’re a seasoned blogger seeking to scale your output or a business owner aiming to maintain an active […]
Error: Metadata-Generation-Failed. Encountered Error While Generating Package Metadata
In the world of software development, encountering errors is an inevitable part of the process. One such error that developers may come across is “Metadata-Generation-Failed,” a message indicating a hiccup in the generation of package metadata. In this article, we’ll delve into the causes of this error, its implications, and effective strategies to troubleshoot and […]
Is It Safe to Download off of Fmovies?
Fmovies has been a popular online platform for streaming movies and TV shows. However, as users seek more convenience, the question arises: Is it safe to download content from Fmovies? In this article, we’ll explore the potential risks associated with downloading from Fmovies and provide insights into maintaining online safety. Understanding Fmovies Fmovies is […]
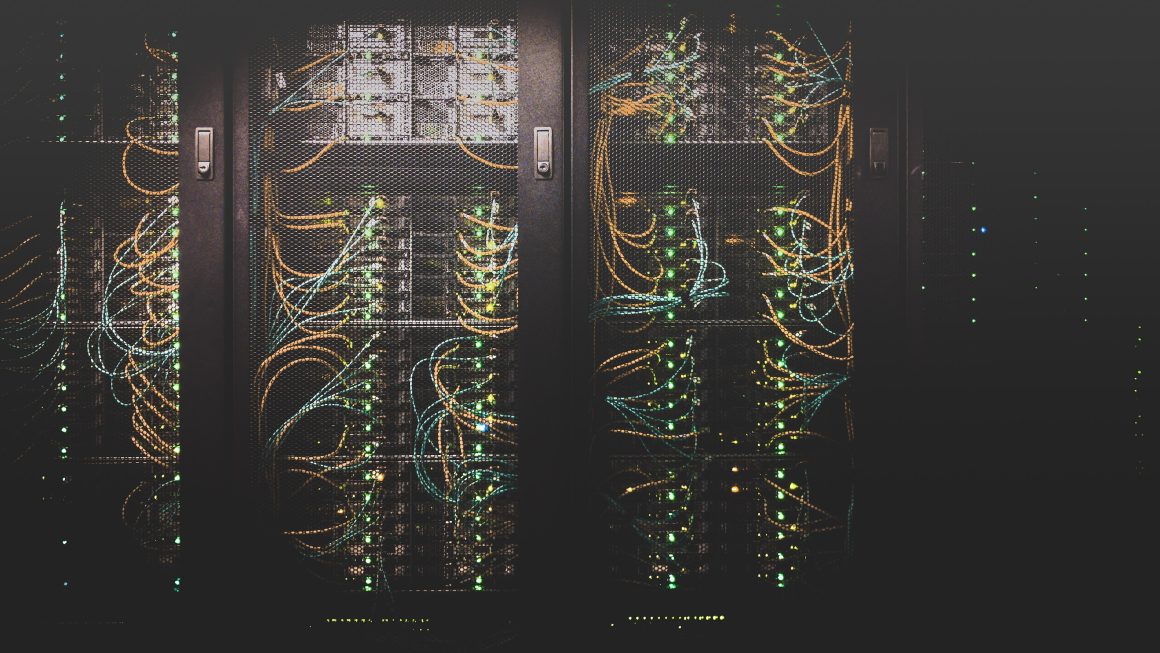
How to setup an Nginx reverse proxy server example
Are you tired of constantly battling with server overload and slow response times? Do you dream of a seamless, efficient way to manage your web traffic and improve the performance of your applications? Look no further! In this article, we will explore the exciting world of Nginx reverse proxy servers and provide you with a […]
Best Table Rate Shipping plugins for WordPress
Are you a WordPress website owner looking to streamline your shipping process and provide accurate shipping rates to your customers? Look no further! In the world of e-commerce, providing seamless and reliable shipping options is crucial for customer satisfaction and business success. Fortunately, with the plethora of table rate shipping plugins available for WordPress, you […]
5 Character.AI Alternatives Without NSFW Filter
Character.AI, a platform known for its AI-generated characters and images, includes a NSFW (Not Safe For Work) filter to restrict explicit content. However, some users may prefer alternatives that inherently exclude NSFW elements. In this article, we will explore five Character.AI alternatives that provide creative and safe AI-generated content without the need for a specific NSFW […]
123Movies: Is It Safe to Use? Best Alternatives in 2023
123Movies, a well-known platform for streaming movies and TV shows, has been a favorite among users seeking free entertainment. However, the safety and legality of using 123Movies have been subjects of concern. In this comprehensive guide, we’ll delve into the safety aspects of 123Movies, explore the potential risks, and present the best alternatives in 2023 […]
How to cancel Trello premium
Trello has been a game-changer in the world of project management, offering users an intuitive platform for organizing tasks and collaborating with team members. However, as your needs evolve and new competitors enter the market, it’s natural to reassess whether Trello Premium is still the right fit for you. Whether it’s due to budget constraints, […]
How to Login & Use WakeID on iPhone
In today’s interconnected world, having easy and secure access to your educational or work resources is crucial. WakeID, a centralized authentication system used by Wake County Public School System (WCPSS) in North Carolina, provides a seamless way to access various services and resources within the school district. In this comprehensive guide, we will walk you […]
What Is Cleverget Free Version Restriction? Includes 4 Possible Ways To Remove It!
In the realm of productivity tools, Cleverget has emerged as a popular choice for individuals and teams looking to streamline their tasks and projects. However, like many software solutions, Cleverget offers both free and premium versions, each with its own set of features and limitations. In this comprehensive guide, we’ll explore the restrictions of the […]